Bitcoin network
Topic: Finance
 From HandWiki - Reading time: 22 min
From HandWiki - Reading time: 22 min
The Bitcoin network is a peer-to-peer network of nodes which implement the Bitcoin protocol. The protocol itself implements a highly available, public, and decentralized ledger. The nodes verify that each update to the ledger follows the rules of the Bitcoin protocol.
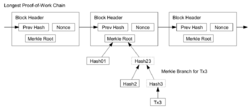
Users broadcast cryptographically signed messages to the network using Bitcoin cryptocurrency wallet software. These messages are proposed transactions, changes to be made in the ledger. Each node has a copy of the ledger's entire transaction history. If a transaction violates the rules of the Bitcoin protocol, it is ignored. Transactions only happen when the full network agrees they should happen. This "full network consensus" is achieved when each node on the network verifies the results of a proof-of-work operation called mining. Mining packages groups of transactions into blocks, and produces a hash code that follows the rules of the Bitcoin protocol. Creating this hash requires expensive energy, but a network node can verify the hash is valid using very little energy. If a miner proposes a block to the network, and its hash is valid, the block and its ledger changes are added to the blockchain, and the network moves on to yet unprocessed transactions. In case there is a dispute, then the longest chain is considered to be correct.
A new block is created every 10 minutes, on average.
Satoshi Nakamoto, the anonymous designer of the protocol, stated that design and coding of Bitcoin began in 2007. The project was released in 2009 as open source software.
The network requires minimal structure to share transactions. An ad hoc decentralized network of volunteers is sufficient. Messages are broadcast on a best-effort basis, and nodes can leave and rejoin the network at will. Upon reconnection, a node downloads and verifies new blocks from other nodes to complete its local copy of the blockchain.[1][2]
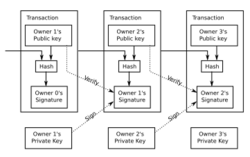
Transactions


A bitcoin is defined by a sequence of digitally signed transactions that began with the bitcoin's creation, as a block reward. The owner of a bitcoin transfers it by digitally signing it over to the next owner using a bitcoin transaction, much like endorsing a traditional bank check. A payee can examine each previous transaction to verify the chain of ownership. Unlike traditional check endorsements, bitcoin transactions are irreversible, which eliminates risk of chargeback fraud.
Although it is possible to handle bitcoins individually, it would be unwieldy to require a separate transaction for every bitcoin in a transaction. Transactions are therefore allowed to contain multiple inputs and outputs, allowing bitcoins to be split and combined. Common transactions will have either a single input from a larger previous transaction or multiple inputs combining smaller amounts, and one or two outputs: one for the payment, and one returning the change, if any, to the sender. Any difference between the total input and output amounts of a transaction goes to miners as a transaction fee.[1]
Mining


To form a distributed timestamp server as a peer-to-peer network, bitcoin uses a proof-of-work system.[2] This work is often called bitcoin mining.
During mining, practically the entire computing power of the Bitcoin network is used to solve cryptographic tasks, the proof of work. Their purpose is to ensure that the generation of valid blocks involves a certain amount of effort, so that subsequent modification of the block chain, such as in the 51% attack scenario, can be practically ruled out. Because of the difficulty, miners form "mining pools" to get payouts despite these high power requirements, costly hardware deployments, and/or hardware under their own control. The largest proportion of mining pools are based in China, which is also where most of the miners—or about 75% of the computing power—of the cryptocurrency are based.[3]
Requiring a proof of work to accept a new block to the blockchain was Satoshi Nakamoto's key innovation. The mining process involves identifying a block that, when hashed twice with SHA-256, yields a number smaller than the given difficulty target. While the average work required increases in inverse proportion to the difficulty target, a hash can always be verified by executing a single round of double SHA-256.
For the bitcoin timestamp network, a valid proof of work is found by incrementing a nonce until a value is found that gives the block's hash the required number of leading zero bits. Once the hashing has produced a valid result, the block cannot be changed without redoing the work. As later blocks are chained after it, the work to change the block would include redoing the work for each subsequent block. If there is a deviation in consensus then a blockchain fork can occur.
Majority consensus in bitcoin is represented by the longest chain, which required the greatest amount of effort to produce. If a majority of computing power is controlled by honest nodes, the honest chain will grow fastest and outpace any competing chains. To modify a past block, an attacker would have to redo the proof-of-work of that block and all blocks after it and then surpass the work of the honest nodes. The probability of a slower attacker catching up diminishes exponentially as subsequent blocks are added.[2]
To compensate for increasing hardware speed and varying interest in running nodes over time, the difficulty of finding a valid hash is adjusted roughly every two weeks. If blocks are generated too quickly, the difficulty increases and more hashes are required to make a block and to generate new bitcoins.[2]
Difficulty and mining pools

Bitcoin mining is a competitive endeavor. An "arms race" has been observed through the various hashing technologies that have been used to mine bitcoins: basic central processing units (CPUs), high-end graphics processing units (GPUs), field-programmable gate arrays (FPGAs) and application-specific integrated circuits (ASICs) all have been used, each reducing the profitability of the less-specialized technology. Bitcoin-specific ASICs are now the primary method of mining bitcoin and have surpassed GPU speed by as much as 300-fold. The difficulty of the mining process is periodically adjusted to the mining power active on the network. As bitcoins have become more difficult to mine, computer hardware manufacturing companies have seen an increase in sales of high-end ASIC products.[4]
Computing power is often bundled together or "pooled" to reduce variance in miner income. Individual mining rigs often have to wait for long periods to confirm a block of transactions and receive payment. In a pool, all participating miners get paid every time a participating server solves a block. This payment depends on the amount of work an individual miner contributed to help find that block, and the payment system used by the pool.[5]
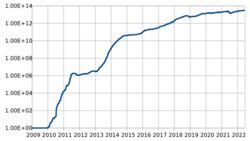
Energy sources and consumption

In 2013, Mark Gimein estimated electricity consumption to be about 40.9 megawatts (982 megawatt-hours a day).[7] In 2014, Hass McCook estimated 80.7 megawatts (80,666 kW). As of 2015[update], The Economist estimated that even if all miners used modern facilities, the combined electricity consumption would be 166.7 megawatts (1.46 terawatt-hours per year).[8] The Cambridge Bitcoin Electricity Consumption Index estimates the energy use of the bitcoin network grew from 1.95 terawatt-hours per year at the end of 2014, to 77.1 terawatt-hours per year by the end of 2019.[6]
Seeking lower electricity costs, some bitcoin miners have set up in places like Iceland where geothermal energy is cheap and cooling Arctic air is free.[9] Chinese bitcoin miners are known to use hydroelectric power in Tibet to reduce electricity costs.[10] North American companies are utilizing stranded gas as a cost-effective source of energy for bitcoin mining.[11] In West Texas, wind powers bitcoin mining.[12] As of April 2021, at least one-third of Bitcoin mining was powered by coal in China's Xinjiang region.[13]
A 2021 study found that carbon emissions from Bitcoin mining in China—where a majority of the proof-of-work algorithm that generated economic value was computed prior to mid-2021[14]—had accelerated rapidly in the late 2010s, are largely fueled by nonrenewable sources and was expected to exceed total annual emissions of countries like Italy and Spain during 2016, interfering with international climate change mitigation commitments.[15][16] It was also found that in 2021, bitcoin mining consumed more energy than the country of New Zealand.[17] A formal Chinese ban on cryptocurrency mining operations in May 2021—reiterated in both September and November—resulted in the relocation of a large majority of mining equipment away from China. Yet as many as 20 percent of "all the world's bitcoin miners remain in China. This is well off its peak of around 65% to 75% of the global market."[14] By December 2021, the global hashrate had mostly recovered to a level before China's crackdown, with increased shares of the total mining power coming from the U.S. (35.4%), Kazakhstan (18.1%), and Russia (11%) instead.[18]
Process

Here are the basic steps of the Bitcoin mining process:
- Acquiring mining hardware: Bitcoin mining requires specialized hardware called ASICs, which are designed specifically for mining Bitcoin. These devices are expensive and consume a lot of electricity.
- Joining a mining pool: Most Bitcoin miners join a mining pool to increase their chances of successfully mining a block. Mining pools are groups of miners who work together to solve complex mathematical problems and share the rewards.
- Installing mining software: Once the hardware is set up and the mining pool is joined, miners need to install mining software on their computers. This software connects the miner's hardware to the mining pool and the Bitcoin network.
- Solving mathematical problems: The mining software instructs the hardware to solve complex mathematical problems called hash functions. These problems require a lot of computing power to solve, and the first miner to solve the problem earns the right to add the next block to the blockchain.
- Verification: Once a miner solves a block, it needs to be verified by other nodes on the Bitcoin network. This is done through a process called consensus, where other nodes in the network confirm that the block is valid and the transactions it contains are legitimate.
- Reward: Miners who successfully solve a block are rewarded with newly minted bitcoins and any transaction fees associated with the block. The current reward for mining a block is 6.25 bitcoins, and the reward is halved every 210,000 blocks, or roughly every four years.
- Continuation: The mining process continues, with new blocks added to the blockchain approximately every ten minutes. The difficulty of the mathematical problems that need to be solved is adjusted every 2016 blocks, or roughly every two weeks, to maintain a consistent rate of block production.
Mined bitcoins
By convention, the first transaction in a block is a special transaction that produces new bitcoins owned by the creator of the block. This is the incentive for nodes to support the network.[1] It provides the way to move new bitcoins into circulation. The reward for mining halves every 210,000 blocks. It started at 50 bitcoin, dropped to 25 in late 2012 and to 12.5 bitcoin in 2016. The most recent halving, which occurred in May 2020 (with block number 630,000), reduced the block reward to 6.25 bitcoin. This halving process is programmed to continue a maximum 64 times before new coin creation ceases.[19]
Security
Various potential attacks on the bitcoin network and its use as a payment system, real or theoretical, have been considered. The bitcoin protocol includes several features that protect it against some of those attacks, such as unauthorized spending, double spending, forging bitcoins, and tampering with the blockchain. Other attacks, such as theft of private keys, require due care by users.[20][21]
Unauthorized spending
Unauthorized spending is mitigated by bitcoin's implementation of public-private key cryptography. For example, when Alice sends a bitcoin to Bob, Bob becomes the new owner of the bitcoin. Eve, observing the transaction, might want to spend the bitcoin Bob just received, but she cannot sign the transaction without the knowledge of Bob's private key.[21]
Double spending
A specific problem that an internet payment system must solve is double-spending, whereby a user pays the same coin to two or more different recipients. An example of such a problem would be if Eve sent a bitcoin to Alice and later sent the same bitcoin to Bob. The bitcoin network guards against double-spending by recording all bitcoin transfers in a ledger (the blockchain) that is visible to all users, and ensuring for all transferred bitcoins that they have not been previously spent.[21]: 4
Race attack
If Eve offers to pay Alice a bitcoin in exchange for goods and signs a corresponding transaction, it is still possible that she also creates a different transaction at the same time sending the same bitcoin to Bob. By the rules, the network accepts only one of the transactions. This is called a race attack, since there is a race between the recipients to accept the transaction first. Alice can reduce the risk of race attack stipulating that she will not deliver the goods until Eve's payment to Alice appears in the blockchain.[22]
A variant race attack (which has been called a Finney attack by reference to Hal Finney) requires the participation of a miner. Instead of sending both payment requests (to pay Bob and Alice with the same coins) to the network, Eve issues only Alice's payment request to the network, while the accomplice tries to mine a block that includes the payment to Bob instead of Alice. There is a positive probability that the rogue miner will succeed before the network, in which case the payment to Alice will be rejected. As with the plain race attack, Alice can reduce the risk of a Finney attack by waiting for the payment to be included in the blockchain.[23]
History modification
Each block that is added to the blockchain, starting with the block containing a given transaction, is called a confirmation of that transaction. Ideally, merchants and services that receive payment in bitcoin should wait for at least a few confirmations to be distributed over the network before assuming that the payment was done. The more confirmations that the merchant waits for, the more difficult it is for an attacker to successfully reverse the transaction—unless the attacker controls more than half the total network power, in which case it is called a 51% attack, or a majority attack.[24] Although more difficult for attackers of a smaller size, there may be financial incentives that make history modification attacks profitable.[25]
Deanonymisation of clients
Deanonymisation is a strategy in data mining in which anonymous data is cross-referenced with other sources of data to re-identify the anonymous data source. Along with transaction graph analysis, which may reveal connections between bitcoin addresses (pseudonyms),[20][26] there is a possible attack[27] which links a user's pseudonym to its IP address. If the peer is using Tor, the attack includes a method to separate the peer from the Tor network, forcing them to use their real IP address for any further transactions. The cost of the attack on the full bitcoin network was estimated to be under €1500 per month, as of 2014.[27]
Payment verification
Each miner can choose which transactions are included in or exempted from a block.[28] A greater number of transactions in a block does not equate to greater computational power required to solve that block.[28]
Upon receiving a new transaction a node must validate it: in particular, verify that none of the transaction's inputs have been previously spent. To carry out that check, the node needs to access the blockchain. Any user who does not trust his network neighbors, should keep a full local copy of the blockchain, so that any input can be verified.
As noted in Nakamoto's whitepaper, it is possible to verify bitcoin payments without running a full network node (simplified payment verification, SPV). A user only needs a copy of the block headers of the longest chain, which are available by querying network nodes until it is apparent that the longest chain has been obtained; then, get the Merkle tree branch linking the transaction to its block. Linking the transaction to a place in the chain demonstrates that a network node has accepted it, and blocks added after it further establish the confirmation.[1]
Data in the blockchain
While it is possible to store any digital file in the blockchain, the larger the transaction size, the larger any associated fees become. The more information that is stored on each block means more information is stored on nodes, potentially creating "blockchain bloating."[29] The first block of the Bitcoin blockchain, known as the "Genesis Block", contains a famous newspaper headline that may hint at Bitcoin's mission.[30] Various items have been embedded, including URLs to websites, an ASCII art image of Ben Bernanke, material from the Wikileaks cables, prayers from bitcoin miners, and the original bitcoin whitepaper.[31] Other important information is stored in the blockchain as well. In Blockchain: Insights You Need from Harvard Business Review, Tapscott, Lakhani, and Iansiti state "With blockchain, we can imagine a world in which contracts are embedded in digital code and stored in transparent, shared databases, where they are protected from deletion, tampering, and revision. Intermediaries like lawyers, brokers, and bankers might no longer be necessary. Individuals, organizations, machines, and algorithms would freely transact and interact with one another with little friction."[32]
Criminal activity
The use of bitcoin by criminals has attracted the attention of financial regulators, legislative bodies, law enforcement, and the media.[33] The FBI prepared an intelligence assessment,[34] the SEC has issued a pointed warning about investment schemes using virtual currencies,[33] and the U.S. Senate held a hearing on virtual currencies in November 2013.[35]
Several news outlets have asserted that the popularity of bitcoins hinges on the ability to use them to purchase illegal goods.[36][37] In 2014, researchers at the University of Kentucky found "robust evidence that computer programming enthusiasts and illegal activity drive interest in bitcoin, and find limited or no support for political and investment motives."[38]
Black markets
A Carnegie Mellon University researcher estimated that in 2012, 4.5% to 9% of all transactions on all exchanges in the world were for drug trades on a single dark web drugs market, Silk Road.[39] Child pornography,[40] murder-for-hire,[41] and weapons[42] are also allegedly available on black market sites that sell in bitcoin. Due to the anonymous nature and the lack of central control on these markets, it is hard to know whether the services are real or just trying to take the bitcoins.[43]
Several deep web black markets have been shut by authorities. In October 2013 Silk Road was shut down by U.S. law enforcement,[44][45][46] leading to a short-term decrease in the value of bitcoin.[47] In 2015, the founder of the site was sentenced to life in prison.[48] Alternative sites were soon available, and in early 2014 the Australian Broadcasting Corporation reported that the closure of Silk Road had little impact on the number of Australians selling drugs online, which had actually increased.[49] In early 2014, Dutch authorities closed Utopia, an online illegal goods market, and seized 900 bitcoins.[50] In late 2014, a joint police operation saw European and American authorities seize bitcoins and close 400 deep web sites including the illicit goods market Silk Road 2.0.[51] Law enforcement activity has resulted in several convictions. In December 2014, Charlie Shrem was sentenced to two years in prison for indirectly helping to send $1 million to the Silk Road drugs site,[52] and in February 2015, its founder, Ross Ulbricht, was convicted on drugs charges and given a sentence of double life imprisonment plus 40 years.[53]
Some black market sites may seek to steal bitcoins from customers. The bitcoin community branded one site, Sheep Marketplace, as a scam when it prevented withdrawals and shut down after an alleged bitcoins theft.[54] In a separate case, escrow accounts with bitcoins belonging to patrons of a different black market were hacked in early 2014.[55]
According to the Internet Watch Foundation, a UK-based charity, bitcoin is used to purchase child pornography, and almost 200 such websites accept it as payment. Bitcoin is not the sole way to purchase child pornography online, as Troels Oertling, head of the cybercrime unit at Europol, states, "Ukash and paysafecard... have [also] been used to pay for such material." However, the Internet Watch Foundation lists around 30 sites that exclusively accept bitcoins.[40] Some of these sites have shut down, such as a deep web crowdfunding website that aimed to fund the creation of new child porn.[56][better source needed] Furthermore, hyperlinks to child porn websites have been added to the blockchain as arbitrary data can be included when a transaction is made.[57][58]
Money laundering
Bitcoins may not be ideal for money laundering, because all transactions are public.[59] Authorities—including the European Banking Authority,[60] the FBI,[34] National Treasury (South Africa)[61] and the Financial Action Task Force of the G7[62]—have expressed concerns that bitcoin may be used for money laundering.
In early 2014, an operator of a U.S. bitcoin exchange, Charlie Shrem, was arrested for money laundering.[63] Subsequently, he was sentenced to two years in prison for "aiding and abetting an unlicensed money transmitting business".[52]
Alexander Vinnik, an alleged owner of BTC-e, was arrested in Greece on 25 July 2017, on $4 billion money laundering charges for flouting anti-money laundering (AML) laws of the US. A report by the UK's Treasury and Home Office named "UK national risk assessment of money laundering and terrorist financing" (October 2015) found that, of the twelve methods examined in the report, bitcoin carries the lowest risk of being used for money laundering, with the most common money laundering method being the banks.[64]
Roman Sterlingov was arrested on 27 April 2021 for allegedly laundering about 1.2 million BTC or US$336 million. According to reports from IRS Criminal Investigation, Sterlingov was the principal operator of a Cryptocurrency tumbler Bitcoin Fog, launched in 2011.[65]
Ponzi scheme
In a Ponzi scheme using bitcoins, the Bitcoin Savings and Trust promised investors up to 7% weekly interest, and raised at least 700,000 bitcoins from 2011 to 2012.[66] In July 2013, the U.S. Securities and Exchange Commission charged the company and its founder in 2013 "with defrauding investors in a Ponzi scheme involving bitcoin".[66]
See also
References
- ↑ 1.0 1.1 1.2 1.3 Nakamoto, Satoshi (24 May 2009). "Bitcoin: A Peer-to-Peer Electronic Cash System". http://bitcoin.org/bitcoin.pdf.
- ↑ 2.0 2.1 2.2 2.3 "Bitter to Better – how to make Bitcoin a better currency". Financial Cryptography and Data Security (Springer Publishing) 7397: 399–414. 2012. doi:10.1007/978-3-642-32946-3_29. ISBN 978-3-642-32945-6. http://crypto.stanford.edu/~xb/fc12/bitcoin.pdf.
- ↑ Jiang, Shangrong; Li, Yuze; Lu, Quanying; Hong, Yongmiao; Guan, Dabo; Xiong, Yu; Wang, Shouyang (2021-04-06). "Policy assessments for the carbon emission flows and sustainability of Bitcoin blockchain operation in China" (in en). Nature Communications 12 (1): 1938. doi:10.1038/s41467-021-22256-3. ISSN 2041-1723. PMID 33824331. Bibcode: 2021NatCo..12.1938J.
- ↑ "Bitcoin boom benefiting TSMC: report". Taipei Times. 4 January 2014. http://www.taipeitimes.com/News/biz/archives/2014/01/04/2003580449.
- ↑ Rosenfeld, Meni (November 17, 2011). Analysis of Bitcoin Pooled Mining Reward Systems. Bibcode: 2011arXiv1112.4980R.
- ↑ 6.0 6.1 "Cambridge Bitcoin Electricity Consumption Index (CBECI)". https://www.cbeci.org/.
- ↑ Gimein, Mark (13 April 2013). "Virtual Bitcoin Mining Is a Real-World Environmental Disaster". Bloomberg Business (Bloomberg LP). https://www.bloomberg.com/news/articles/2013-04-12/virtual-bitcoin-mining-is-a-real-world-environmental-disaster.
- ↑ "The magic of mining". The Economist. 13 January 2015. https://www.economist.com/news/business/21638124-minting-digital-currency-has-become-big-ruthlessly-competitive-business-magic.
- ↑ O'Brien, Matt (13 June 2015). "The scam called Bitcoin". Daily Herald. http://www.dailyherald.com/article/20150613/business/150619551/.
- ↑ Potenza, Alessandra (21 December 2017). "Can renewable power offset bitcoin's massive energy demands?". TheVerge News. https://www.theverge.com/2017/12/21/16806772/bitcoin-cryptocurrency-energy-consumption-renewables-climate-change.
- ↑ Yang, Stephanie (29 March 2019). "Bitcoin in the wilderness". The Wall Street Journal. https://www.wsj.com/articles/bitcoin-in-the-wilderness-11553860802.
- ↑ Orcutt, Mike (27 February 2020). "How Texas's wind boom has spawned a Bitcoin mining rush". MIT Technology Review. https://www.technologyreview.com/2020/02/27/905626/how-texass-wind-boom-has-spawned-a-bitcoin-mining-rush/.
- ↑ "Commentary: How much Bitcoin comes from dirty coal? A flooded mine in China just spotlighted the issue" (in en). https://fortune.com/2021/04/20/bitcoin-mining-coal-china-environment-pollution/.
- ↑ 14.0 14.1 "Inside China's underground crypto mining operation, where people are risking it all to make bitcoin". CNBC. 18 December 2021. https://www.cnbc.com/2021/12/18/chinas-underground-bitcoin-miners-.html.
- ↑ Lu, Donna. "Bitcoin mining emissions in China will hit 130 million tonnes by 2024". New Scientist. https://www.newscientist.com/article/2273672-bitcoin-mining-emissions-in-china-will-hit-130-million-tonnes-by-2024/.
- ↑ Jiang, Shangrong; Li, Yuze; Lu, Quanying; Hong, Yongmiao; Guan, Dabo; Xiong, Yu; Wang, Shouyang (6 April 2021). "Policy assessments for the carbon emission flows and sustainability of Bitcoin blockchain operation in China" (in en). Nature Communications 12 (1): 1938. doi:10.1038/s41467-021-22256-3. ISSN 2041-1723. PMID 33824331. Bibcode: 2021NatCo..12.1938J.
 Available under CC BY 4.0.
Available under CC BY 4.0.
- ↑ Browne, Ryan (2021-02-05). "Bitcoin's wild ride renews worries about its massive carbon footprint" (in en). https://www.cnbc.com/2021/02/05/bitcoin-btc-surge-renews-worries-about-its-massive-carbon-footprint.html.
- ↑ Mellor, Sophie (9 December 2021). "Bitcoin miners have returned to the record activity they had before China's crypto crackdown" (in en). Fortune. https://fortune.com/2021/12/09/bitcoin-miners-hashrate-record-activity-china-crypto-crackdown-kazakhstan/.
- ↑ Antonopoulos, Andreas M (1 July 2017). Mastering bitcoin: programming the open blockchain (2nd ed.). Sebastopol, California, USA: O'Reilly Media. pp. 239. ISBN 978-1-4919-5438-6. OCLC 953432201.
- ↑ 20.0 20.1 Ron Dorit; Adi Shamir (2012). "Quantitative Analysis of the Full Bitcoin Transaction Graph". Cryptology ePrint Archive. http://eprint.iacr.org/2012/584.pdf.
- ↑ 21.0 21.1 21.2 "Bitcoin: A Primer for Policymakers". Mercatus Center. George Mason University. 2013. http://mercatus.org/sites/default/files/Brito_BitcoinPrimer.pdf.
- ↑ Erik Bonadonna (29 March 2013). "Bitcoin and the Double-spending Problem". Cornell University. http://blogs.cornell.edu/info4220/2013/03/29/bitcoin-and-the-double-spending-problem/.
- ↑ Karame, Ghassan O.; Androulaki, Elli; Capkun, Srdjan (2012). Two Bitcoins at the Price of One? Double-Spending Attacks on Fast Payments in Bitcoin. International Association for Cryptologic Research. http://eprint.iacr.org/2012/248.pdf. Retrieved 22 October 2014.
- ↑ Michael J. Casey; Paul Vigna (16 June 2014). "Short-Term Fixes To Avert "51% Attack"". Money Beat (Wall Street Journal). https://blogs.wsj.com/moneybeat/2014/06/16/bitbeat-a-51-attack-what-is-it-and-could-it-happen/.
- ↑ Bar-Zur, Roi; Abu-Hanna, Ameer; Eyal, Ittay; Tamar, Aviv (2023). WeRLman: To Tackle Whale (Transactions), Go Deep (RL). IEEE Computer Society. doi:10.1109/SP46215.2023.00016. https://doi.ieeecomputersociety.org/10.1109/SP46215.2023.00016. Retrieved 15 May 2023.
- ↑ Reid, Fergal; Harrigan, Martin (2013). "An Analysis of Anonymity in the Bitcoin System". Security and Privacy in Social Networks: 197–223. doi:10.1007/978-1-4614-4139-7_10. ISBN 978-1-4614-4138-0.
- ↑ 27.0 27.1 Biryukov, Alex; Khovratovich, Dmitry; Pustogarov, Ivan (2014). "Deanonymisation of clients in Bitcoin P2P network". ACM Conference on Computer and Communications Security. ISBN 9781450329576. Bibcode: 2014arXiv1405.7418B. http://orbilu.uni.lu/handle/10993/18679.
- ↑ 28.0 28.1 Houy, N. (2016). "The Bitcoin Mining Game". Ledger 1: 53–68. doi:10.5195/ledger.2016.13. http://www.ledgerjournal.org/ojs/index.php/ledger/article/view/13/59. Retrieved 14 January 2017.
- ↑ Ali, Saqib; Wang, Guojun; White, Bebo; Cottrell, Roger Leslie (2018-09-06). "A Blockchain-Based Decentralized Data Storage and Access Framework for PingER" (in English). IEEE International Conference on Trust, Security and Privacy in Computing and Communications (Online) 2018: 1303–1308. doi:10.1109/trustcom/bigdatase.2018.00179. ISBN 978-1-5386-4388-4. ISSN 2324-9013. https://www.osti.gov/pages/biblio/1475405.
- ↑ "Genesis Block Definition" (in en). https://www.investopedia.com/terms/g/genesis-block.asp.
- ↑ "How porn links and Ben Bernanke snuck into Bitcoin's code". CNN. 2 May 2013. https://money.cnn.com/2013/05/02/technology/security/bitcoin-porn/.
- ↑ Tapscott1, Lakhani2, Iansiti3, Don1, Karim R.2, Marco3 (2019). Blockchain : insights you need from Harvard Business Review.. Boston: Harvard Business Review Press. pp. 12. ISBN 9781633697911. OCLC 1083823199. http://worldcat.org/oclc/1083823199.
- ↑ 33.0 33.1 Lavin, Tim (8 August 2013). "The SEC Shows Why Bitcoin Is Doomed". bloomberg.com (Bloomberg LP). http://www.bloombergview.com/articles/2013-08-08/did-the-sec-just-validate-bitcoin-no-.
- ↑ 34.0 34.1 "Bitcoins Virtual Currency: Unique Features Present Challenges for Deterring Illicit Activity". Cyber Intelligence Section and Criminal Intelligence Section (FBI). 24 April 2012. https://www.wired.com/images_blogs/threatlevel/2012/05/Bitcoin-FBI.pdf.
- ↑ Lee, Timothy B. (21 November 2013). "Here's how Bitcoin charmed Washington". The Washington Post. https://www.washingtonpost.com/news/the-switch/wp/2013/11/21/heres-how-bitcoin-charmed-washington/.
- ↑ "Monetarists Anonymous". The Economist (The Economist Newspaper Limited). 29 September 2012. http://www.economist.com/node/21563752.
- ↑ Ball, James (22 March 2013). "Silk Road: the online drug marketplace that officials seem powerless to stop Limited". The Guardian. https://www.theguardian.com/world/2013/mar/22/silk-road-online-drug-marketplace.
- ↑ Matthew Graham Wilson; Aaron Yelowitz (November 2014). "Characteristics of Bitcoin Users: An Analysis of Google Search Data". Social Science Research Network Working Papers Series.
- ↑ Christin, Nicolas (2013). "Traveling the Silk Road: A Measurement Analysis of a Large Anonymous Online Marketplace". Carnegie Mellon INI/CyLab. p. 8. http://www.andrew.cmu.edu/user/nicolasc/publications/Christin-WWW13.pdf. Retrieved 22 October 2013. "we suggest to compare the estimated total volume of Silk Road transactions with the estimated total volume of transactions at all Bitcoin exchanges (including Mt. Gox, but not limited to it). The latter corresponds to the amount of money entering and leaving the Bitcoin network, and statistics for it are readily available... approximately 1,335,580 BTC were exchanged on Silk Road... approximately 29,553,384 BTC were traded in Bitcoin exchanges over the same period... The only conclusion we can draw from this comparison is that Silk Road-related trades could plausibly correspond to 4.5% to 9% of all exchange trades"
- ↑ 40.0 40.1 Schweizer, Kristen (10 October 2014). "Bitcoin Payments by Pedophiles Frustrate Child Porn Fight". BloombergBusiness (Bloomberg LP). https://www.bloomberg.com/news/articles/2014-10-09/bitcoin-payments-by-pedophiles-frustrate-child-porn-fight.
- ↑ Lake, Eli (17 October 2013). "Hitman Network Says It Accepts Bitcoins to Murder for Hire". The Daily Beast. The Daily Beast Company LLC. http://www.thedailybeast.com/articles/2013/10/17/hitman-network-says-it-accepts-bitcoins-to-murder-for-hire.html.
- ↑ Smith, Gerry (15 April 2013). "How Bitcoin Sales Of Guns Could Undermine New Rules". HuffPost. http://www.huffingtonpost.com/2013/04/15/bitcoin-guns_n_3070828.html.
- ↑ Alex, Knapp (19 January 2015), "Faking Murders And Stealing Bitcoin: Why The Silk Road Is The Strangest Crime Story Of The Decade", Forbes, https://www.forbes.com/sites/alexknapp/2015/01/19/faking-murders-and-stealing-bitcoin-why-the-silk-road-is-the-strangest-crime-story-of-the-decade/, retrieved 2 January 2016
- ↑ Andy Greenberg (23 October 2013). "FBI Says It's Seized $28.5 Million In Bitcoins From Ross Ulbricht, Alleged Owner Of Silk Road" (blog). Forbes. https://www.forbes.com/sites/andygreenberg/2013/10/25/fbi-says-its-seized-20-million-in-bitcoins-from-ross-ulbricht-alleged-owner-of-silk-road/. Retrieved 24 November 2013.
- ↑ Kelion, Leo (12 February 2014). "Five arrested in Utopia dark net marketplace crackdown". BBC. https://www.bbc.co.uk/news/technology-26158012.
- ↑ Alex Hern (3 October 2013). "Bitcoin price plummets after Silk Road closure". The Guardian. https://www.theguardian.com/technology/2013/oct/03/bitcoin-price-silk-road-ulbricht-value. "Digital currency loses quarter of value after arrest of Ross Ulbricht, who is accused of running online drugs marketplace"
- ↑ Robert McMillan (2 October 2013). "Bitcoin Values Plummet $500M, Then Recover, After Silk Road Bust". Wired. https://www.wired.com/2013/10/bitcoin-market-drops-600-million-on-silk-road-bust/. Retrieved 31 October 2014.
- ↑ "Silk Road drug website founder Ross Ulbricht jailed". BBC News. 29 May 2015. https://www.bbc.com/news/world-us-canada-32941060.
- ↑ Katie Silver (31 March 2014). "Silk Road closure fails to dampen illegal drug sales online, experts say". ABC News. http://www.abc.net.au/news/2014-03-31/online-drug-trade-soaring-experts-say/5354930.
- ↑ Sophie Murray-Morris (13 February 2014). "Utopia no more: Drug marketplace seen as the next Silk Road shut down by Dutch police". The Independent (London). https://www.independent.co.uk/life-style/gadgets-and-tech/utopia-no-more-drug-marketplace-seen-as-the-next-silk-road-shut-down-by-dutch-police-9126063.html.
- ↑ Wakefield, Jane (7 November 2014). "Huge raid to shut down 400-plus dark net sites". BBC. https://www.bbc.com/news/technology-29950946.
- ↑ 52.0 52.1 Nate Raymond (19 December 2014). "Bitcoin backer gets two years prison for illicit transfers". Reuters (Thompson Reuters). https://www.reuters.com/article/us-usa-crime-bitcoin-idUSKBN0JX2CW20141219.
- ↑ "Ross Ulbricht: Silk Road creator convicted on drugs charges". BBC. 5 February 2015. https://www.bbc.com/news/world-us-canada-31134938.
- ↑ Ravi Mandalia (1 December 2013). "Silk Road-like Sheep Marketplace scams users; over 39k Bitcoins worth $40 million stolen". Techie News. http://www.techienews.co.uk/973470/silk-road-like-sheep-marketplace-scams-users-39k-bitcoins-worth-40-million-stolen/.
- ↑ "Silk Road 2 loses $2.7m in bitcoins in alleged hack". BBC News. 14 February 2014. https://www.bbc.co.uk/news/technology-26187725.
- ↑ "While Markets Get Seized: Pedophiles Launch a Crowdfunding Site". http://www.deepdotweb.com/2014/11/09/as-drug-markets-are-seized-pedophiles-launch-a-crowdfunding-site/.
- ↑ Hopkins, Curt (7 May 2013). "If you own Bitcoin, you also own links to child porn". The Daily Dot. http://www.dailydot.com/business/bitcoin-child-porn-transaction-code/.
- ↑ Bradbury, Danny. "As Bitcoin slides, the Blockchain grows". IET Engineering and Technology Magazine. http://eandt.theiet.org/magazine/2015/02/in-blocks-we-trust.cfm.
- ↑ Kirk, Jeremy (28 August 2013). "Bitcoin offers privacy-as long as you don't cash out or spend it". PC World. http://www.pcworld.com/article/2047608/bitcoin-offers-privacy-as-long-as-you-dont-cash-out-or-spend-it.html.
- ↑ "Warning to consumers on virtual currencies". European Banking Authority. 12 December 2013. http://www.eba.europa.eu/documents/10180/16136/EBA+Warning+on+Virtual+Currencies.pdf.
- ↑ "IFWG Crypto Assets Working Group". National Treasury, Republic of South Africa. http://www.treasury.gov.za/comm_media/press/2021/IFWG_CAR%20WG_Crypto%20assets%20FAQs_Final.pdf.
- ↑ "Guidance for a Risk-Based Approach: Prepaid Cards, Mobile Payments and Internet-based Payment Services". Guidance for a risk-based approach. Paris: Financial Action Task Force (FATF). June 2013. p. 47. http://www.fatf-gafi.org/media/fatf/documents/recommendations/Guidance-RBA-NPPS.pdf.
- ↑ Lee, Dave (27 January 2014). "US makes Bitcoin exchange arrests after Silk Road closure". BBC. https://www.bbc.co.uk/news/technology-25919482.
- ↑ "UK national risk assessment of money laundering and terrorist financing". UK HM Treasury and Home Office. https://www.gov.uk/government/uploads/system/uploads/attachment_data/file/468210/UK_NRA_October_2015_final_web.pdf.
- ↑ Delevingne, Lawrence (28 April 2021). "U.S. arrests alleged 'Bitcoin Fog' money launderer - Reuters" (in en). https://www.reuters.com/technology/us-arrests-alleged-bitcoin-fog-money-launderer-2021-04-28/.
- ↑ 66.0 66.1 "SEC charges Texas man with running Bitcoin-denominated Ponzi scheme" (Press release). US Securities and Exchange Commission. 23 July 2013. Retrieved 7 March 2014.
 KSF
KSF