Aurora Generator Test
 From Wikipedia - Reading time: 8 min
From Wikipedia - Reading time: 8 min

Idaho National Laboratory ran the Aurora Generator Test in 2007 to demonstrate how a cyberattack could destroy physical components of the electric grid.[1] The experiment used a computer program to rapidly open and close a diesel generator's circuit breakers out of phase from the rest of the grid, thereby subjecting the engine to abnormal torques and ultimately causing it to explode. This vulnerability is referred to as the Aurora Vulnerability.
This vulnerability is especially a concern because most grid equipment supports using Modbus and other legacy communications protocols that were designed without security in mind. As such, they do not support authentication, confidentiality, or replay protection. This means that any attacker that can communicate with the device can control it and use the Aurora Vulnerability to destroy it.
Experiment
[edit]To prepare for the experiment, the researchers procured and installed a 2.25 MW (3000 horsepower) generator and connected it to the substation. They also needed access to a programmable digital relay or another device capable of controlling the breaker. Although such access can be through a mechanical or digital interface, in this case the latter was used.[2][3]
A generator unit consists of a diesel engine mechanically linked to an alternator. In many commercial-industrial settings, multiple generators need to operate together in tandem, in order to provide power to the desired load. A generator that is operating normally is synchronized with either the power grid or with one or more additional generators (for example in an "islanded" independent power network as might be used in a remote location or for emergency backup power). When generators are operating in synchronicity, effectively their alternators are magnetically locked together.[4]
In the Aurora experiment, the researchers used a cyberattack to open and close the breakers out of sync, in order to deliberately maximize the stress. Each time the breakers were closed, the torque induced in the alternator (as a result of the out-of-synchrony connection) caused the entire generator to bounce and shake. The generator used in the experiment was equipped with a resilient rubber rotating coupling (located between the diesel engine and the alternator, thus indirectly connecting the engine's steel crankshaft to the alternator's steel shaft).[3][5]
During the initial steps of the attack, black rubber pieces were ejected as the rotating coupling was incrementally destroyed (as a result of the extremely abnormal torques induced by the out-of-synchronization alternator on the diesel engine's crankshaft).[5] The rotating rubber coupling was soon destroyed outright, whereupon the diesel engine itself was then quickly ripped apart, with parts sent flying off.[6] Some parts of the generator landed as far as 80 feet away from the generator.[7] In addition to the massive and obvious mechanical damage to the diesel engine itself, evidence of overheating of the alternator was later observed (upon subsequent disassembly of the unit).[3]
In this attack, the generator unit was destroyed in roughly three minutes. However, this process took three minutes only because the researchers assessed the damage from each iteration of the attack. A real attack could have destroyed the unit much more quickly.[6] For example, a generator built without a rotating rubber coupling between the diesel engine and the alternator would experience the crankshaft-destroying abnormal forces in its diesel engine immediately, given the absence of a shock-absorbing material between these two rotating components. A generator unit assembled in this way could see its diesel engine ruined by a single out-of-synchrony connection of the alternator.[5]
The Aurora experiment was designated as unclassified, for official use only.[8] On September 27, 2007, CNN published an article based on the information and video DHS released to them,[1] and on July 3, 2014, DHS released many of the documents related to the experiment as part of an unrelated FOIA request.[5]
Vulnerability
[edit]The Aurora vulnerability is caused by the out-of-sync closing of the protective relays.[6]
"A close, but imperfect, analogy would be to imagine the effect of shifting a car into Reverse while it is being driven on a highway, or the effect of revving the engine up while the car is in neutral and then shifting it into Drive."[6]
"The Aurora attack is designed to open a circuit breaker, wait for the system or generator to slip out of synchronism, and reclose the breaker, all before the protection system recognizes and responds to the attack... Traditional generator protection elements typically actuate and block reclosing in about 15 cycles. Many variables affect this time, and every system needs to be analyzed to determine its specific vulnerability to the Aurora attack... Although the main focus of the Aurora attack is the potential 15-cycle window of opportunity immediately after the target breaker is opened, the overriding issue is how fast the generator moves away from system synchronism."[9]
Potential impact
[edit]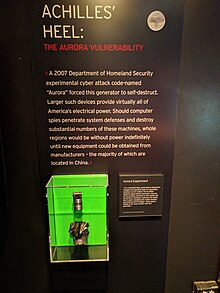
The failure of even a single generator could cause widespread outages and possibly cascading failure of the entire power grid as occurred in the Northeast blackout of 2003. Additionally, even if there are no outages from the removal of a single component (N-1 resilience), there is a large window for a second attack or failure as it could take more than a year to replace a destroyed generator, because many generators and transformers are custom-built.
Mitigations
[edit]The Aurora vulnerability can be mitigated by preventing the out-of-phase opening and closing of the breakers. Some suggested methods include adding functionality in protective relays to ensure synchronism and adding a time delay for closing breakers.[10]
One mitigation technique is to add a synchronism-check function to all protective relays that potentially connect two systems together. To implement this, the function must prevent the relay from closing unless the voltage and frequency are within a pre-set range.
Devices such as the IEEE 25 Sync-Check relay and IEEE 50 can be used to prevent out-of-phase opening and closing of the breakers.[11]
Diesel engines can also be equipped with independent sensors that detect abnormal vibration signatures. It is possible to design such a sensor to immediately trigger a complete shutdown of the generator upon detection of a single major excursion from the vibration signature of a normally operating engine.[12] However, the damage from that single excursion might already be substantial, particularly if a resilient rubber coupling between the engine and the alternator is not present.
Criticisms
[edit]There was some discussion as to whether Aurora hardware mitigation devices (HMD) can cause other failures. In May 2011, Quanta Technology published an article that used RTDS (Real Time Digital Simulator) testing to examine the "performance of multiple commercial relay devices available" of Aurora HMDs. To quote: "The relays were subject to different test categories to find out if their performance is dependable when they need to operate, and secure in response to typical power system transients such as faults, power swing and load switching... In general, there were technical shortcomings in the protection scheme’s design that were identified and documented using the real time testing results. RTDS testing showed that there is, as yet, no single solution that can be widely applied to any case, and that can present the required reliability level."[13] A presentation from Quanta Technology and Dominion succinctly stated in their reliability assessment "HMDs are not dependable, nor secure."[14]
Joe Weiss, a cybersecurity and control system professional, disputed the findings from this report and claimed that it has misled utilities. He wrote: "This report has done a great deal of damage by implying that the Aurora mitigation devices will cause grid issues. Several utilities have used the Quanta report as a basis for not installing any Aurora mitigation devices. Unfortunately, the report has several very questionable assumptions. They include applying initial conditions that the hardware mitigation was not designed to address such as slower developing faults, or off nominal grid frequencies. Existing protection will address “slower” developing faults and off nominal grid frequencies (<59 Hz or >61 Hz). The Aurora hardware mitigation devices are for the very fast out-of-phase condition faults that are currently gaps in protection (i.e., not protected by any other device) of the grid."[15]
Timeline
[edit]On March 4, 2007, Idaho National Laboratory demonstrated the Aurora vulnerability.[16]
On June 21, 2007, NERC notified industry about the Aurora vulnerability.[17]
On September 27, 2007, CNN released a previously classified demonstration video of the Aurora attack on their homepage.[1] That video can be downloaded from here.
On October 13, 2010, NERC released a recommendation to industry on the Aurora vulnerability.[17]
On July 3, 2014, the US Department of Homeland Security released 840 pages of documents related to Aurora in response to an unrelated FOIA request.[5]
See also
[edit]- Brittle Power
- Electromagnetic pulse
- Energy security
- List of power outages
- New York City blackout of 1977
- Programmable logic controller
- Resilient control systems
- Vulnerability of nuclear plants to attack
- When Technology Fails
- Metcalf sniper attack
References
[edit]- ^ a b c "Mouse click could plunge city into darkness, experts say". CNN. September 27, 2007. Retrieved January 30, 2020.
- ^ "FOIA Request - Operation Aurora" (PDF). Muckrock. p. 91. Retrieved January 30, 2020.
- ^ a b c Greenberg, Andy (October 23, 2020). "How 30 Lines of Code Blew Up a 27-Ton Generator". Wired. Retrieved December 11, 2021.
- ^ Greenberg, Andy (October 23, 2020). "How 30 Lines of Code Blew Up a 27-Ton Generator". Wired. Retrieved December 11, 2021.
- ^ a b c d e "FOIA Request - Operation Aurora". Muckrock. 17 May 2014. Retrieved January 30, 2020.
- ^ a b c d "FOIA Request - Operation Aurora" (PDF). Muckrock. p. 59. Retrieved January 30, 2020.
- ^ "Master Script" (PDF). INTERNATIONAL SPY MUSEUM. p. 217. Retrieved January 30, 2020.
- ^ "FOIA Request - Operation Aurora" (PDF). Muckrock. p. 134. Retrieved January 30, 2020.
- ^ Zeller, Mark. "Common Questions and Answers Addressing the Aurora Vulnerability". Schweitzer Engineering Laboratories, Inc. Retrieved January 30, 2020.
- ^ Zeller, Mark. "Myth or Reality – Does the Aurora Vulnerability Pose a Risk to My Generator?". Schweitzer Engineering Laboratories, Inc. Retrieved January 30, 2020.
- ^ "Avoiding unwanted reclosing on rotating apparatus (Aurora)" (PDF). Power System Relaying and Control Committee. Retrieved January 30, 2020.
- ^ S R W Mills (2010). Vibration Monitoring & Analysis Handbook. British Institute of Non-Destructive Testing.
- ^ "QT e-News" (PDF). Quanta Technology. p. 3. Retrieved January 30, 2020.
- ^ "Aurora Vulnerability Issues & Solutions Hardware Mitigation Devices (HMDs)" (PDF). Quanta Technology. July 24, 2011. Retrieved January 30, 2020.[permanent dead link]
- ^ "Latest Aurora information – this affects ANY electric utility customer with 3-phase rotating electric equipment!". Unfettered Blog. September 4, 2013. Retrieved January 30, 2020.
- ^ "U.S. video shows hacker hit on power grid". USA Today. September 27, 2007. Retrieved January 30, 2020.
- ^ a b "NERC Issues AURORA Alert to Industry" (PDF). NERC. October 14, 2010. Archived from the original (PDF) on 2011-08-12. Retrieved January 30, 2020.
External links
[edit]- Aurora Revisited — by its original project lead - OTbase
- What You Need to Know (and Don’t) About the AURORA Vulnerability - Power
- The All-Too-Real Cyberthreat NOBODY is Prepared for (Aurora) - Breaking Energy
- Simulated attack points to vulnerable U.S. power infrastructure - ComputerWorld
- New docs show DHS was more worried about critical infrastructure flaw in '07 than it let on - ComputerWorld
- DHS Releases Hundreds of Documents on Wrong Aurora Project - Threat post
- July 2014 Archives by thread - infracritical.com
- SECURING THE U.S. ELECTRICAL GRID - thepresidency.org
- Misconceptions about Aurora: Why Isn't More Being Done - InfoSec
- AURORA Vulnerability Background- Southern California Edison (SCE)
 KSF
KSF